✍️ Write for CostObserver
🎁 Get published, get rewarded! Selected posts receive 10 SGD voucher. Share your Cloud Cost Optimization and SecFinOps expertise.
 CostObserver ✦ Now Live
CostObserver ✦ Now LiveInsights on SecFinOps, cloud costs, and AWS optimization
🎁 Get published, get rewarded! Selected posts receive 10 SGD voucher. Share your Cloud Cost Optimization and SecFinOps expertise.
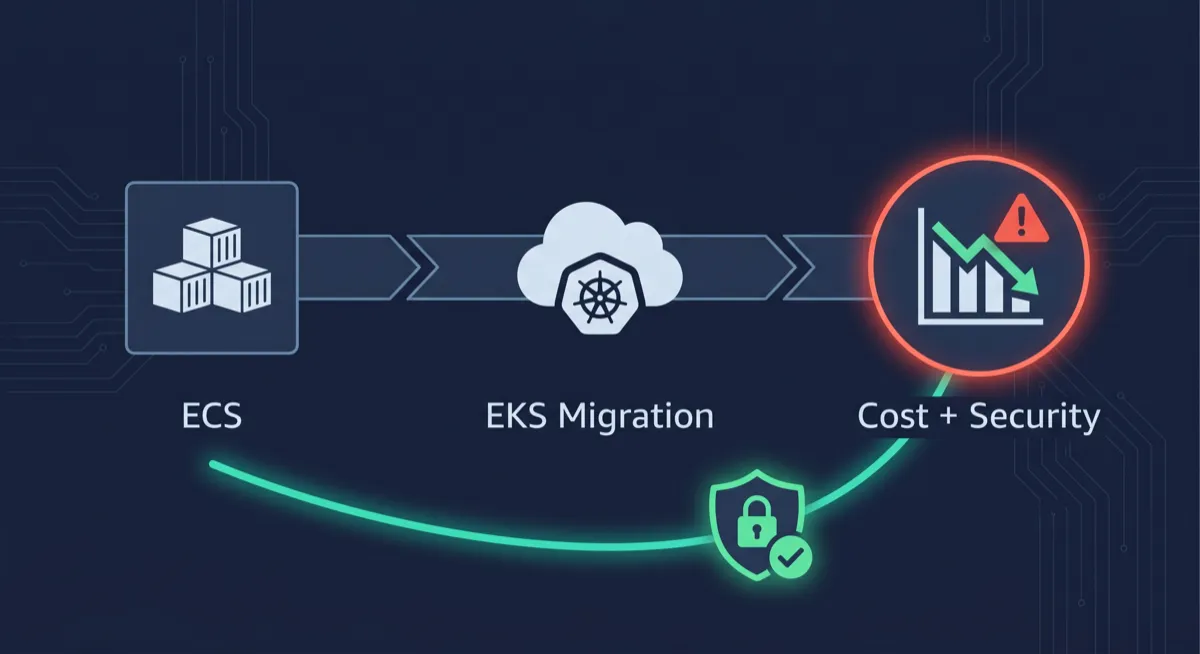
Migrating from ECS to EKS is one of the most effective ways to cut AWS costs. The savings are real. But every architectural decision that reduced your bill also changed your security posture. Most teams measure one and ignore the other.

Your security queue has hundreds of open alerts. Most of them are not costing you anything right now. The ones that are look identical to the ones that are not. That is the prioritisation problem nobody is solving.

Most AWS tagging strategies are built for cost allocation. They answer who owns this resource and what does it cost. They do not answer whether it is safe to optimise, delete, or resize. Here is the tagging model that serves both teams.

When the cloud bill is both a cost problem and a security problem, who actually owns it? The answer is not FinOps. It is not SecOps. It is you.

Two teams. Two dashboards. Two investigations of the same incident. The real cost of keeping FinOps and SecOps separate is not the tools. It is the time, the mistakes, and the compliance violations hiding in the gap between them.

Cost Explorer shows you what you spent. It does not show you why. The gap between those two questions is where security incidents live undetected for weeks.
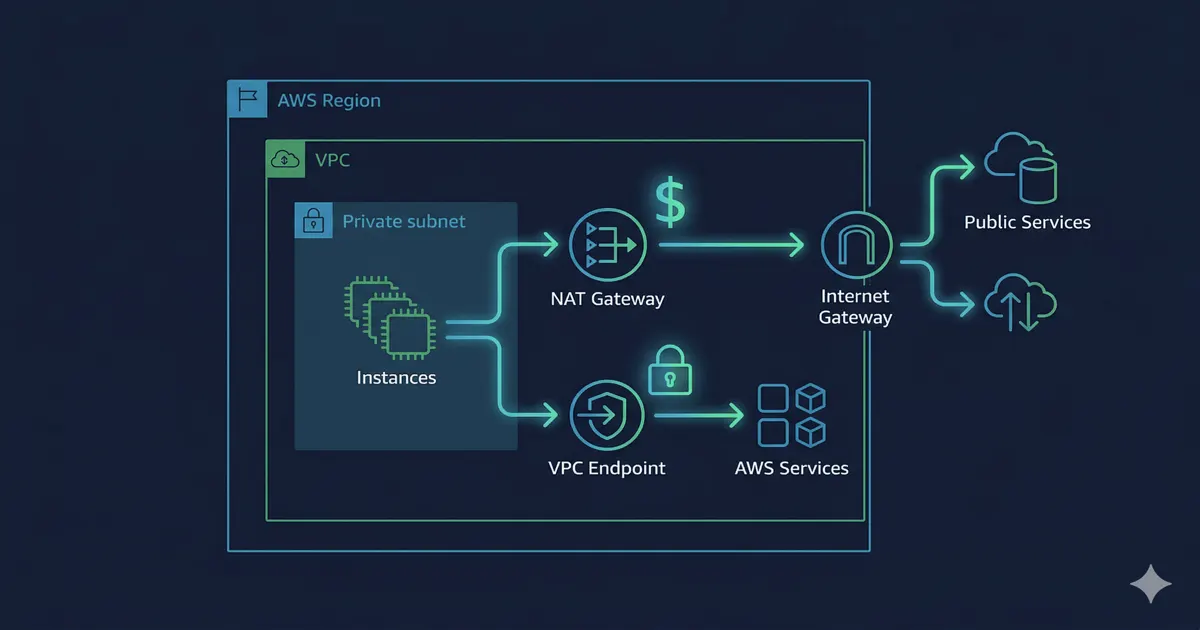
In private-subnet architectures running ECS or EKS, NAT Gateway data processing charges quietly exceed EC2 costs. The fix is a data path decision you probably never made explicitly.
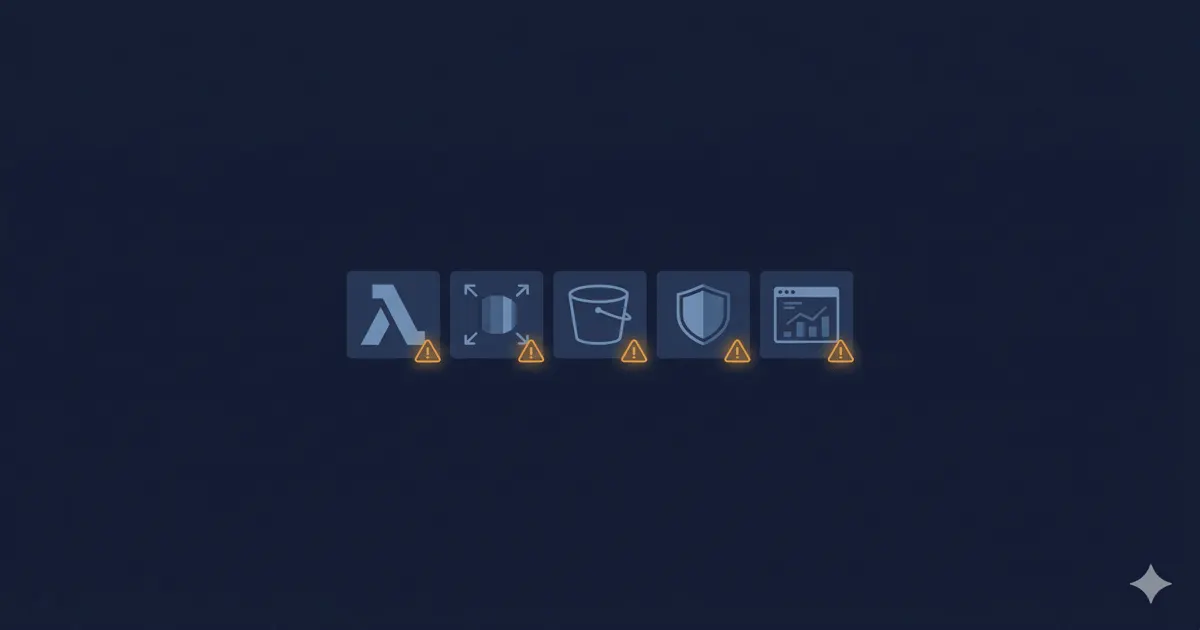
Each of these five misconfigurations has a cost symptom and a security implication. Most teams fix the bill and never ask the security question behind it.

AWS Cost Anomaly Detection is not just a billing tool. Configured correctly, it is an early warning system for compromised credentials, runaway functions, and infrastructure abuse.

The first sign of a compromised AWS credential is almost never a security alert. It is a line item in your billing console that nobody routes to the security team.

You are paying for every malicious request that hits your infrastructure. Your billing console just calls it normal spend. Here is exactly where the hidden tax lives.

Your team has too many alerts. But the real problem is not the volume. It is that severity alone is not enough context to know which ones actually matter right now.
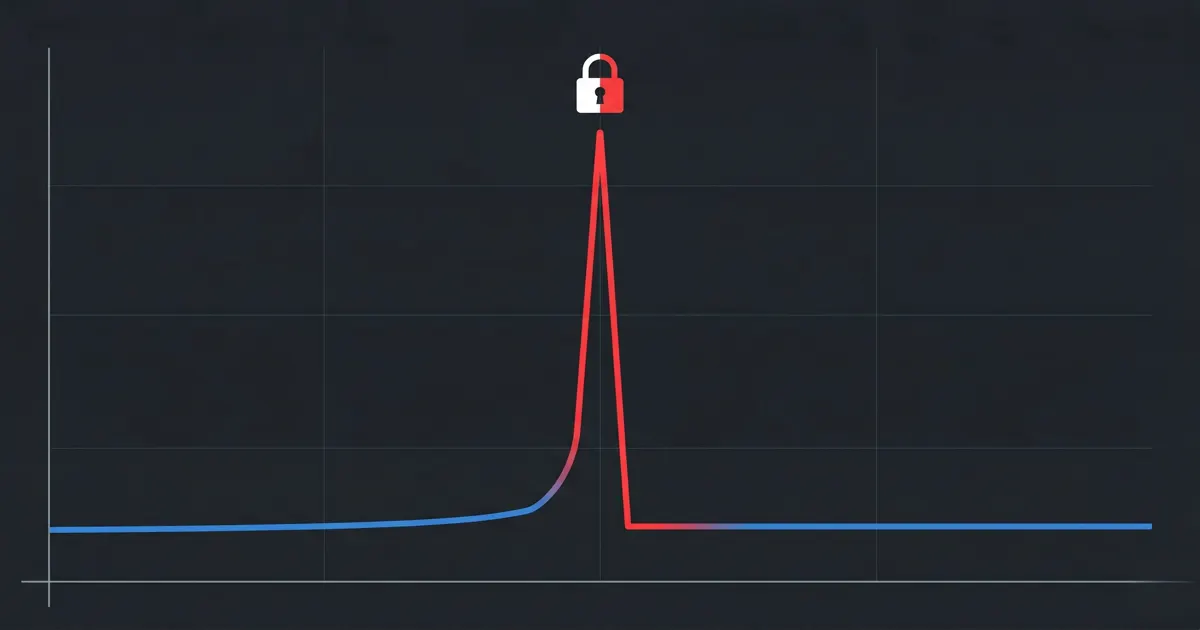
That cost spike last Tuesday? It probably was not your dev team spinning up extra instances. Here is what your billing dashboard is not showing you.

Your FinOps team looks at the bill. Your SecOps team looks at the alerts. Neither team is reading the same story. Here is why that gap exists and what it is costing you.